September 8th, 2014 by Elma Jane
One of the greatest mistake any merchants can do is deciding to lease or rent a credit card terminal rather than getting one for FREE. While the practice of leasing has declined in recent years in the US it is all they are doing in Canada whether the merchant is renting from a bank or leasing from a sales rep. In both the US and Canada some sales reps will still strive and persuade you that leasing is the perfect choice for you. You’re not obliged to pay any cash up front, or You’re assured a substitute terminal if yours breaks. Those selling statements may sound decent, but they’re not. A terminal lease will end up costing you hundreds, if not thousands of dollars more than what it’s worth. With the fees you’ll end up disbursing to lease a terminal, you could buy that same terminal in a matter of months. If you lease a terminal you could also be forced to buy equipment insurance, which is an additional expense. You may even have to give back the terminal at the end of your lease!
Why Purchasing a Credit Card Terminal is a Good Choice
A terminal lease brings with it a 48 month lease contract. That is a lengthy time to be giving for a terminal that doesn’t cost more than $300 today. Why not just buy one entirely? The cost of the purchase is absolutely tax deductible. Even if you can’t come up with the money to pay cash for your terminal, you can just put it on a business credit card. The interest given is still tax deductible, and let’s says you have a 19 percent credit card rate, if you pay the same amount of $/month toward your credit card balance that you would have paid toward your lease, you’ll have the terminal paid off in less than a year. That’s a savings that can be better channelled into budding and growing your company.
FREE Credit Card Terminal
For those of you, who feels that because of the ever changing technology, they do not want to continue buying new terminals, there are FREE Terminals offers all across Canada. So, with your FREE terminals, there is no out of pocket set up expense and your current processing rate can be the same or reduced significantly. If your terminal breaks or if there is a better technology that develops, the company automatically ships to you at no charge an upgraded terminal. So, if you can’t buy one, see if your credit card processor will give you one for FREE.
If you’re stuck in a lease, you most likely won’t able to end the contract. A lease term is usually 48 months, so you’ll have to look up when that term terminates before you can leave without a consequence. As an alternative, do your own research and analyze the total expense of leasing vs. purchasing. Better yet, strongly consider the benefits of not having to worry about anything, at one point is that FREE terminal usually has $25 minimum expense to the merchant. Mom taught you there was no free lunch didn’t she? If you decide to return the FREE terminal, you may find a RETURN EQUIPMENT FEE or an EARLY RETURN FEE of that FREE EQUIPMENT.
Posted in Best Practices for Merchants, Credit Card Reader Terminal Tagged with: bank, card, cash, credit, credit card processor, credit card terminal, credit-card, fees, Merchant's, processor, tax, terminal
September 5th, 2014 by Elma Jane
Businesses are rapidly adopting a third-party operations model that can put payment data at risk. Today, the PCI Security Standards Council, an open global forum for the development of payment card security standards, published guidance to help organizations and their business partners reduce this risk by better understanding their respective roles in securing card data. Developed by a PCI Special Interest Group (SIG) including merchants, banks and third-party service providers, the information supplement provides recommendations for meeting PCI Data Security Standard (PCI DSS) requirement 12.8 to ensure payment data and systems entrusted to third parties are maintained in a secure and compliant manner.
Breach reports continue to highlight security vulnerabilities introduced by third parties as a leading cause of data compromise. The leading mistake organizations make when entrusting sensitive and confidential consumer information to third-party vendors is not applying the same level of rigor to information security in vendor networks as they do in their own. Per PCI DSS Requirement 12.8, if a merchant or entity shares cardholder data with a third- party service provider, certain requirements apply to ensure continued protection of this data will be enforced by such providers. The Third-Party Security Assurance Information Supplement focuses on helping organizations and their business partners achieve this by implementing a robust third-party assurance program.
Produced with the expertise and real-world experience of more than 160 organizations involved in the Special Interest Group, the guidance includes practical recommendations on how to:
Conduct due diligence and risk assessment when engaging third party service providers to help organizations understand the services provided and how PCI DSS requirements will be met for those services.
Develop appropriate agreements, policies and procedures with third-party service providers that include considerations for the most common issues that arise in this type of relationship.
Implement a consistent process for engaging third-parties that includes setting expectations, establishing a communication plan, and mapping third-party services and responsibilities to applicable PCI DSS requirements.
Implement an ongoing process for maintaining and managing third-party relationships throughout the lifetime of the engagement, including the development of a robust monitoring program.
The guidance includes high-level suggestions and discussion points for clarifying how responsibilities for PCI DSS requirements may be shared between an entity and its third-party service provider, as well as a sample PCI DSS responsibility matrix that can assist in determining who will be responsible for each specific control area.
PCI Special Interest Groups are PCI community-selected and developed initiatives that provide additional guidance and clarifications or improvements to the PCI Standards and supporting programs. As part of its initial proposal, the group also made specific recommendations that were incorporated into PCI DSS requirements 12.8 and 12.9 in version 3.0 of the standard.One of the big focus areas in PCI DSS 3.0 is security as a shared responsibility. This guidance is an excellent companion document to the standard in helping merchants and their business partners work together to protect consumers’ valuable payment information.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security Tagged with: banks, Breach, card, card data, cardholder, consumer, data, data security, Merchant's, networks, payment, payment card security, payment data, payment information, PCI, PCI-DSS, provider's, Security, Security Assurance, security standards, security standards council, Service providers, services
September 5th, 2014 by Elma Jane
A cup of coffee, a pack of chewing gum., a newspaper at the airport. For even the smallest, most casual purchase, credit cards and debit cards are replacing cash as the preferred form of payment. One in three usually uses a credit card or a debit card for in-person purchases of less than $5. Eleven percent prefer credit cards, 22% debit cards and 65% cash, but the generational divide is striking. A slight majority (51 percent) of consumers 18-29 prefer plastic to cash, the only age group to do so. A preference for cash becomes stronger in each advancing age bracket, until at age 65-plus, 82 percent prefer cash.
Survey conducted by landline and cellphone found that: Credit cards and debit cards are used more frequently for small purchases by those employed full time (42%) or part time (34%) than for the unemployed (23%). People with children are more likely to use the cards for small purchases (41%) than those without children (30%), perhaps because parents have less time to wait around for change. Income doesn’t seem to be much of a differentiator, except for those near the bottom of the scale. A combined 38% of those making $75,000 or more preferred plastic for small purchases, compared with 43 percent of those making $50,000 to $74,900, 32% of those earning $30,000 to $49,900 and only 23% percent of those making less than $30,000.
Politically, we’ve finally found something on which we all can agree. Thirty percent of Democrats and a nearly identical 28% of Republicans favor credit cards or debit cards rather than cash for small purchases. Interestingly, those describing themselves as politically independent also were more independent from cash, 40% of them prefer plastic for such transactions.
The casual use of plastic is moving steadily through age brackets and already has a firm grip not only on millennials, but also increasingly on Gen Xers. Crunched another way, the data show that if you’re 49 or younger, you’re almost as likely to pay for a $5 purchase with plastic as you are to pay with cash. Fifty two percent prefer cash, 46% prefer debit or credit cards. Now, if you’re 50 or older, you’re still somewhat unlikely to pay for a $5 purchase with plastic. Seventy seven percent still prefer cash, with 21% reaching for debit cards or credit cards. Those who graduated from or attended college are significantly more comfortable than others with using plastic for small purchases.
A combined 39% of those with college degrees prefer debit cards (21%) or credit cards (18%) over cash (59%). Only 16% of those who have not attended college usually use debit cards for purchases of less than $5, along with only 6 percent who prefer credit cards for that purpose.
The trend is clear. Regardless of some differences in magnitude based on demographic factors, plastic is replacing cash as the currency of choice even for small purchases. Plastic use will increase for small purchases, both for debit and credit cards.
Why the shift to cards There are many reasons:
Technological advancements at the point of sale have made it just as fast to pay by plastic as by cash. Rewards have become a common feature of credit cards, with two out of three credit cards offering rewards, encouraging rewards chasing. Debit cards, with their balances available instantly and online have largely replaced paper checks and tedious manual records.
Financial institutions have spent decades persuading consumers to use and merchants to accept cards universally. Small purchases represent particularly appropriate uses of a debit card, assuming you don’t get carried away and overdraw the card-linked bank account. Why keep going to the bank and then carry cash if you don’t have to? Moving away from cash and moving toward using cards for even small purchases is more convenient.
Debit cards are everywhere already, but because their use can’t be reported to the credit bureaus and thus, they don’t build credit, they should only be used as a matter of convenience. People who frequently use credit cards for small, casual purchases also could overdo it, but probably not to a great degree. It would take a lot of lattes to send someone into credit counseling or bankruptcy court. In truth, we like the idea of using credit cards frequently for small, manageable expenses. This gives users the benefit of an active credit history, but leaves them with monthly bills that are small enough to pay off in full, so they don’t have to pay any interest. It’s getting to the point where, if I’m out and about, I’m using plastic the whole time. It’s just so much easier.
Posted in Best Practices for Merchants Tagged with: account, bank, bank account, bankruptcy, bills, cards, cash, cellphone, credit, credit counseling, credit history, data, debit cards, financial, financial institutions, Merchant's, payment, transactions
September 4th, 2014 by Elma Jane
EMV, which stands for Europay, MasterCard and Visa, and is slated to be mandated across the United States starting in October 2015 and automated fuel dispensers have until October 2017 to comply. Unlike magnetic swipe cards, EMV chip cards encrypt data and authenticate communication between the card and card reader. Additionally, chip card user is prompted for a PIN for authentication.
Why are those dates important? Companies lose $5.33 billion to fraud today, with card issuers and merchants incurring 63 and 37 percent of these losses, respectively. Under the EMV mandate, merchants who do not process chip cards will bear the burden of the issuer loss. By accepting chip card transactions, merchants and issuers should see a reduction in fraud.
Overcoming Barriers to EMV Adoption
Given the significant barriers to EMV adoption, it may be tempting for merchants to meet minimum requirements for accepting EMV payments. However, medium to large retailers should also consider the bigger picture of customer security and peace of mind.
Some key critical success factors for a payment initiative of this size include:
Business Continuity Architecture: As with all payment systems, it is imperative to have the EMV system running at all times. The solution should preferably have Active-Active architecture across multiple data centers and have a low Recovery Point Objective (the point in time to which the systems and data must be recovered after an outage).
Cost Benefit Analysis: Take a top down approach and decide accordingly on the scope of the analysis. This will ensure that decisions on scope are made on basis of quantitative data and not just qualitative arguments.
Phased Approach: To overcome time or cost overage in a project of this scope and complexity, retailers should try using an iterative approach for development. The rollout can be divided into multiple releases of six to seven months, which will provide the opportunity to review, capture lessons learnt, and improve subsequent releases.
Proactive Monitoring Alerts: Considering the criticality of business function carried out by EMV, tokenization and payment gateway, a vigorous supervising environment must be defined to perform proactive and reactive monitoring. It should take into consideration the monitoring targets, tools, scope and methods. This will provide advance visibility to the failure points and better ensuring maximum system availability.
Resilience Testing: Typically in a software project, the testing is limited to the unit, integration, performance and user acceptance. However, due to the critical nature of the applications and systems involved, robust resiliency testing is vital. This will ensure that there are no single points of failure and the system remains available when running in error conditions.
Stakeholder Identification: This is a key step to ensure that you have varied perspectives from all departments and their support. It will keep your organization from being blindsided and reduce the risk of disagreements in later stages of the program. Key stakeholders should include Store Operations, Card Accounting, Loss Prevention, Contact Center and IT & Data Security.
Organizations should adopt a five step approach to implement a secure, robust and industry-leading payment solution:
Encryption – Point to point encryption will ensure card data is secure and encrypted from the point of capture to the processor. Usually, merchants use data encryption that is not point to point, rendering their organization vulnerable to data breaches. Software encryption is the most common form of encryption, as it is easily installed and quires little or no hardware upgrades; however, it is less secure, may expose encryption keys, and is prone to memory scanning attacks. Hardware encryption is considered more secure but requires more costly terminal upgrades. Hardware encryption is designed to self-destruct the keys if tampered, but is not well-defined as very limited headway has been made in this space.
Tokenization – Build a Card Data Environment (CDE) that will host a centralized card data storage solution. Only limited applications with firewall access and capability to mutually authenticate via certificates can access CDE and receive card data. The rest of the applications will have tokens which are random numbers. This architecture will ease the merchant’s burden with existing and emerging PCI Data Security Standards.
Payment Gateway – Perform a risk assessment on the current payment gateway and identify gaps in functionality, manageability, compliance, scalability, speed to market and best practices. Determine the alternatives to mitigate the risks. Some of the important aspects of a leading payment gateway solution are support for all forms of credit, debit, gift cards and check transactions. Its ability to work with any acquirer, in-built encryption abilities, support for settlement and reconciliation must also be kept into consideration.
Settlement, Funding and Reconciliation – A workflow-based system to handle chargebacks and the automation of chargeback processing will greatly reduce labor-intensive work and enhance the quality of data used for settlement and reconciliation. Upgrades to the existing receipt retrieval system may be needed.
Card fraud is on the rise in the U.S., and merchants are the primary target for stealing information. With the EMV deadline just over a year away, the responsible retailer must take steps to prepare now. Although EMV implementation might seem overwhelming to merchants, they should start their journey to secure payments rather than wait for a looming deadline. Solutions such as data encryption and tokenization should be used in combination with EMV to implement a robust payment solution to better protect merchants against fraud. By proactively adopting EMV payment solutions, merchants can stay ahead of the regulatory curve and better protect their customers from fraud.
Posted in Best Practices for Merchants, Credit Card Security, EMV EuroPay MasterCard Visa, Payment Card Industry PCI Security, Visa MasterCard American Express Tagged with: authentication, automation, card, card data, Card Data Environment, card fraud, card issuers, card transactions, CDE, chargeback, chargeback processing, check, check transactions, chip, chip cards, credit, customer, customer security, data, data breaches, data encryption, data security, debit, EMV, emv chip cards, EuroPay, fraud, gateway, Gift Cards, host, integration, magnetic swipe cards, MasterCard, Merchant's, payment, payment gateway, payment solution, payment systems, PCI, PCI Data Security Standards, PIN, processor, retailers, Security, software, swipe, terminal, tokenization, tools, visa
September 4th, 2014 by Elma Jane
The move to mobile point of sale (mobile POS) is radically changing the face of customer interactions and payments, as both customers and merchants grow increasingly comfortable with the concept of mobile payments. In the current, crowded marketplace most mobile payment solutions are not compatible with each other. Instead of unifying the payment experience they create islands separated by technology or usage that are tailored to individual providers in the market. Multiple devices are currently needed in-store to process different payment types and the challenge is how they can make payments unified in such a way that only one device is needed in store.
The use of cash by customers also adds a level of complication to the mobile POS story. The removal of IDM terminals, removal of customer queues and ability for customers to simply walk up and pay an assistant or to leave a store and have their bank card automatically debited certainly suits the expectations of customers today, however a large number of customers still use traditional cash methods to pay for goods and services. A number of stores that have gone down the route of implementing mobile POS now have a problem dealing with cash because the wandering shop assistants and personal shoppers can only accept card or web-based payment options. The future for mobile POS has potential to be bright, a dominant player will have to emerge in the market. This will break down the technology barriers and usage barriers between different players. The success to mobile POS lies in the payment process being truly unified with one device in one place and very seamless workflow. This will be very complicated thing to achieve, there have been a lot of attempts and a lot of false starts in the history of mobile POS. MPOS will be the future. Five years from now people will be amazed that they did transactions with landlines. NO child will ever see a telephone with a cord attached. Never a popcorn on top of the stove since we developed microwave ovens. Technology changes, and we are slow to adopt new stuff. Once we change we don’t know how we did without it.
Posted in Best Practices for Merchants, Mobile Payments, Mobile Point of Sale, Point of Sale, Smartphone Tagged with: bank, card, cash, customer, devices, IDM terminals, Merchant's, mobile, mobile point of sale, MPOS, payment solutions, payment types, payments, point of sale, POS, provider's, services, technology, terminals, web-based payment
August 28th, 2014 by Elma Jane
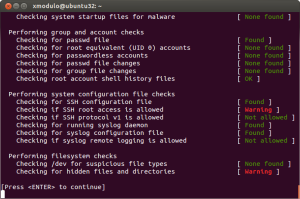
Merchants are still using pedestrian passwords that crooks can easily break, security company Trustwave has found. Of the nearly 630,000 stored passwords that Trustwave obtained during penetration tests in the past two years, its technicians were able to crack more than half in just a few minutes and 92% within 31 days. Even though adding new information about weak passwords or ongoing malware investigations gets frustrating because the same problems facing the financial and payments industries persist, it does not surprise Trustwave researchers. For a lot of software or hardware developers, their main concern is availability of the service. They want to make sure their POS is available and running to accept credit cards, often at the cost of a lot of security controls. It is difficult to implement security and to do it correctly.
Trustwave recommends longer passwords with more characters, rather than shorter ones with letters and numbers. A longer password that is a phrase not easily figured out is better than a shorter, complex password. These findings have been added to an online version of the 2014 Trustwave Global Security Report. To accommodate the fast changing nature of security threats, Trustwave is regularly updating its research and making the information available to consumers and payments industry stakeholders on the company’s site. The criminals stealing data are a constantly moving target. It no longer made sense for those interested in our research to have to wait a year to see new statistics. Having access to updated security reporting should be helpful to merchants. They can see how trends are tracking over time, instead of constantly having to go online to see what is relevant to them or rely on the trade groups to keep them informed. This provides one switch to keep them in the know, so there is some value there and it’s a smart move on Trustwave’s part. Since the new Payment Card Industry security requirements call for security measures to be embedded in software development lifecycles, there is some utility in Trustwave’s new approach to sharing research information.
Trustwave said the trend of businesses detecting breaches continues to rise, with 29% of businesses doing so in 2013 compared to only 9% in 2009. Trustwave compiled that data from 691 post-breach forensics investigations conducted in 2013. The report also indicated e-commerce breaches are increasing, with 54% of all breaches targeting e-commerce sites in 2013, compared to only 9% in 2010. More regions, including the U.S., being in various stages of converting to EMV chip-based cards for card-present transactions fuels the criminals’ shift to e-commerce fraud. Additionally, the company is working with law enforcement officials after discovering a control center of eight servers behind what is being called Magnitude, an exploit kit of Russian origin that has led to thousands of attacks and millions of attempted malware attacks globally.
Posted in Best Practices for Merchants, Payment Card Industry PCI Security, Point of Sale Tagged with: breaches, card, card-present transactions, company, credit cards, data, e-commerce, EMV chip-based cards, financial, fraud, Global Security, hardware, industry, Malware, Merchant's, online, passwords, payment, Payment Card Industry security, payments, payments industries, POS, Security, servers, software
August 27th, 2014 by Elma Jane
Backoff malware that has attacked point of sale systems at hundreds of businesses may accelerate adoption of EMV chip and PIN cards and two-factor authentication as merchants look for ways to soften the next attack. Chip and PIN are a big thing, because it greatly diminishes the value of the information that can be trapped by this malware, said Trustwave, a security company that estimates about 600 businesses have been victims of the new malware. The malware uses infected websites to infiltrate the computing devices that host point of sale systems or are used to make payments, such as PCs, tablets and smartphones. Merchants can install software that monitors their payments systems for intrusions, but the thing is you can’t just have anti-virus programs and think you are safe. Credit card data is particularly vulnerable because the malware can steal data directly from the magnetic stripe or keystrokes used to make card payments.
The point of sale system is low-hanging fruit because a lot of businesses don’t own their own POS system. They rent them, or a small business may hire a third party to implement their own point of sale system. The Payment Card Industry Security Standards Council issued new guidance this month to address security for outsourced digital payments. EMV-chip cards, which are designed to deter counterfeiting, would gut the value of any stolen data. With this magnetic stripe data, the crooks can clone the card and sell it on the black market. With chip and PIN, the data changes for each transaction, so each transaction is unique. Even if the malware grabs the data, there not a lot the crooks can do with it. The EMV transition in the U.S. has recently accelerated, driven in part by recent highprofile data breaches. Even with that momentum, the U.S. may still take longer than the card networks’ October 2015 deadline to fully shift to chip-card acceptance.
EMV does not by itself mitigate the threat of breaches. Two-factor authentication, or the use of a second channel or computing device to authorize a transaction, will likely share in the boost in investment stemming from data security concerns. The continued compromise of point of sale merchants through a variety of vectors, including malware such as Backoff, will motivate the implementation among merchants of stronger authentication to prevent unauthorized access to card data.
Backoff has garnered a lot of attention, including a warning from the U.S. government, but it’s not the only malware targeting payment card data. It is not the types of threats which are new, but rather the frequency with which they are occurring which has put merchants on their heels. There is also an acute need to educate small merchants on both the threats and respective mitigation techniques.. The heightened alert over data vulnerability should boost the card networks’ plans to replace account numbers with substitute tokens to protect digital payments. Tokens would not necessarily stop crooks from infiltrating point of sale systems, but like EMV technology, they would limit the value of the stolen data. There are two sides to the equation, the issuers and the merchants. To the extent we see both sides adopt tokenization, you will see fewer breaches and they will be less severe because the crooks will be getting a token instead of card data.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security, Point of Sale Tagged with: access, account, account numbers, anti-virus programs, authentication, Backoff, card, card networks, chip, credit, Credit card data, credit-card, data, data breaches, devices, digital payments, EMV, magnetic stripe, Malware, Merchant's, Payment Card Industry, payments, PCs, PIN, PIN cards, point of sale, POS, POS system, programs, Security, security standards, Smartphones, software, system, tablets, tokenization, tokens, transaction, Trustwave, websites
August 25th, 2014 by Elma Jane
Let’s talk about success stories of the people who worked with National Transaction and made it big in this field. One great story that we have is about Big Daddy. I named this guy Big Daddy, because of the great success that he made in this industry. Big Daddy was a Physical fitness trainer with an outgoing personality before he joined National Transaction. He gained knowledge about the card industry and build a good working relationship with NTC’s President Mr. M. Together, they secure a relationship with several associations and negotiated a deal. Now, they were able to partner with a high risk account. While these associations continue to profit from the relationship, Big Daddy took 3 years off. These associations assist merchants become more profitable and is the leading global advocate for travel agents, the travel industry and the traveling public, also the world’s largest association of travel professionals. National Transaction has been ASTA member and a partner since then for almost 10 years now. As Big Daddy broaden his knowledge and skills about the industry, he started to build his own portfolio which gave him the ability to form his residual income. As of this date, he averages $30,000 monthly with National Transaction, while running his own business. If Big Daddy made it, then other Sales Representatives can make it bigger too. With the right company to work with like National Transaction, right tools and full support from our Team and Customer Service your on the right track, so why not make a move??? Start building your portfolio and give it a shot or if you already have one, work it out. You will never know. In all labor there is a profit.
Posted in nationaltransaction.com Tagged with: account, ASTA, card, card industry, customer service, high risk account, Merchant's, National Transaction, residual, residual income, sales, travel, travel agents
August 21st, 2014 by Elma Jane
Package delivery giant UPS has become the latest company to admit that customer payment card details may be at risk after it discovered malware at 51 of its US stores. In a statement, UPS says that customers who used credit and debit cards at 51 of its 4470 franchised sites between 20 January and 11 August are at risk. Names, postal and email addresses and payment card information may all be compromised, but UPS says that it has no evidence of any fraud, and that the malware has now been eliminated. Earlier this month the US government took the step of putting out an alert warning retailers about a new family of malware, dubbed Backoff, targeting point-of-sale systems. The UPS Store, received a bulletin from the government among many other US retailers that made them aware of the problem. As soon as they became aware of the potential malware intrusion, they deployed extensive resources to quickly address and eliminate the issue. Customers can be assured that they have identified and fully contained the incident. US merchants have found themselves under siege from hackers in recent months, with the most notable case seeing thieves use a vendor’s credentials to infect POS devices with malware and steal the details of around 40 million Target customer cards.
Posted in Best Practices for Merchants, Credit Card Security Tagged with: card, card details, card information, credit, customer, customer cards, debit cards, devices, fraud, Malware, Merchant's, payment, point of sale, POS, retailers
August 21st, 2014 by Elma Jane
Accept Electronic Payments in Their Currency, Convert it to Yours. National Transaction helps you and your customers transact with confidence.
DCC provides convenient currency conversion service at the time of purchase benefiting both the credit card holder and merchants. Our solution provides a system where the Visa or MasterCard holder in a foreign country can shop on an American based website that displays prices in their own local currency. Dynamic Currency Conversion utilizes a Bank Reference Table (BRT) otherwise known as a Card Recognition Table (CRT). This table is updated on a daily basis so that transactions have the most up to date conversion rate for transactions. Your web site holds pricing information in $USD, and based on the selection of the shopper, prices are converted to their native currency. At the close of the transaction an invoice or receipt can present the total to the customer in their currency, along with the merchants local currency along with the exchange rate that was applied.Your business reaches foreign nations expanding your market while presenting new opportunities, increasing your businesses bottom line and making international transaction with confidence. We have diverse set of applications to enable various kinds of business models and financial frameworks.
Posted in Best Practices for Merchants Tagged with: Bank Reference, Card Recognition, conversion rate, credit-card, currency, Currency Conversion, customers, DCC, Dynamic Currency, electronic payments, exchange rate, financial, invoice, MasterCard, Merchant's, pricing, rate, receipt, transactions, visa, website