September 21st, 2016 by Elma Jane
PCI compliance applies to any company, organization or merchant of any size or transaction volume that either accepts, stores or transmits cardholder data.
Any merchant accepting payments directly from the customer via credit or debit card must be Compliant. The merchant themselves are therefore responsible for becoming Compliant, as the deadline for the merchant becomes overdue.
Understanding and knowing the details of Payment Card Industry Compliance can help you better prepare your business. Because failing and waiting to become compliant or ignoring them, could end up being an expensive mistake.
The VISA regulations have to adhere to the PCI standard forms as part of the operating regulations. The regulations signed when you open an account at the bank. The rules under which merchants are allowed to operate merchant accounts.
The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security, Visa MasterCard American Express Tagged with: American Express, cardholder, compliance, credit, customer, data, debit card, Discover, jcb, MasterCard, merchant, Payment Card Industry, payments, PCI, transaction, visa

February 2nd, 2016 by Elma Jane
Businesses continue to struggle with the prohibited storage of unencrypted customer payment data. The Payment Card Industry Data Security Standard (PCI DSS), merchants are instructed that, Protection methods are critical components of cardholder data protection in PCI DSS Requirement.
PCI DSS applies to every company that stores, processes or transmits cardholder information. Regardless of the size or type of business you operate, the number of credit card transactions you process annually or the method you use to do so, you must be PCI compliant.
Data breach is not a limited, one-time occurrence. This is why PCI compliance is required across all systems used by merchants.
Encryption and Tokenization is a strong combination to protect cardholder at all points in the transaction lifecycle; in use, in transit and at rest.
National Transaction’s security solutions provide layers of protection, when used in combination with EMV and PCI-DSS compliance.
Encryption is ideally suited for any businesses that processes card transactions in a face to face or card present environment. From the moment a payment card is swiped or inserted at a terminal featuring a hardware-based, tamper resistant security module, encryption protects the card data from fraudsters as it travels across various systems and networks until it is decrypted at secure data center.
Tokenization can be used in card not present environments (travel merchants) such as e-commerce or mail order/telephone order (MOTO), or in conjunction with encryption in card present environments. Tokens can reside on your POS/PMS or within your e-commerce infrastructure at rest and can be used to make adjustments, add new charges, make reservations, perform recurring transactions, or perform other transactions in use. Tokenization protects card data when it’s in use and at rest. It converts or replaces cardholder data with a unique token ID to be used for subsequent transactions.
The sooner businesses implement encryption and tokenization the sooner stored unencrypted data will become a thing of the past.
Posted in Best Practices for Merchants, Travel Agency Agents Tagged with: card, card data, card present, cardholder, compliance, credit card, customer, data, data breach, data security, e-commerce, EMV, encryption, Mail Order/Telephone Order, merchants, moto, payment, Payment Card Industry, PCI-DSS, POS, secure data, Security, terminal, tokenization, tokens, travel, travel merchants

October 15th, 2015 by Elma Jane
There are numbers of guidelines issued for accepting card payments, and merchants are expected to understand them all. To avoid issues down the road know a few basic rules in order to keep your business going without being penalized.
There’s a lot of ways to process a credit card: In-store, online, and by phone. There’s also different ways to pay and different brands of cards.
In-store and Card-not-present policies.
In-Store Policies:
- Always verify that the person presenting the card is the cardholder
- Ask for a 2nd ID for comparison
- Cards are non-transferable, cardholder MUST be present for purchase
- Compare the signature on the back of the card with that of the person who presents the card
- Inspect the card to confirm that it’s not visibly altered or mutilated
- Validate the card’s expiration date
Online/Phone Payment Policies: Card-not-present transactions
- Card account number
- Card billing address
- CID (3 digits on back of card OR 4 on the front)
- Card expiration date
- Card member’s home or billing telephone number
- Card member name (as it appears on the Card)
Rules for Visa, MasterCard and Amex that merchants need to know:
- Never store cardholder data on any systems to help minimize the risk of fraud and protect your business from potential chargebacks.
Complying with Federal Laws, State Laws and PCI
- A merchant should be familiar with and abide by Federal Laws regarding accepting credit cards. The Fair Credit Reporting Act is the federal law that establishes the foundation of consumer credit rights. This law regulates the collection and use of consumer credit information by merchants.
- Check state laws on the use of consumer credit information and accepting credit cards. Not all states have additional laws that regulate credit card practices, but some (such as California) prohibit merchants from requesting/requiring a customer to provide any personal information (like their address or telephone number) on any form involved with their credit card transaction. So, it is advised that merchants inquire about further information in their particular state.
- The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements designed to ensure that all companies processing, storing, or transmitting credit card information uphold a secure environment. These rules essentially apply to any merchant that has a Merchant ID (MID). If you are a merchant that accepts credit card payments, you are required to comply with the PCI Data Security Standard, large or small businesses.
EMV Liability Shift Set By Visa and MasterCard as of October 1st
U.S. banks and credit card companies are now using the EMV (Europay, MasterCard, and Visa) technology. The EMV liability shift for fraud carried out in physical stores with counterfeit cards belongs to the merchant if it has not yet upgraded its POS system to accept EMV-enabled chip cards. While issuers absorb losses under card-network rules, that burden will shift to acquirers in cases where the fraud occurs at merchants unprepared for EMV.
It’s good to know every aspect of your business. The above guidelines are part of a business that every merchants should be familiar with. The main reason for these rules is to protect your business and keep your customer’s payment card data safe and secure.
To start accepting more credit cards give us a call now at 888-996-2273. We have the latest terminals that’s EMV/NFC capable.
Posted in Best Practices for Merchants, Credit Card Security, EMV EuroPay MasterCard Visa, Payment Card Industry PCI Security Tagged with: amex, card network, card payments, card-not-present, chargebacks, chip cards, credit card, credit card companies, Data Security Standard, EMV, EuroPay, MasterCard, merchants, MID, Payment Card Industry, PCI-DSS, POS system, U.S. banks, visa

October 9th, 2015 by Elma Jane
Credit card fraud is much more difficult to prevent in a card-not-present transaction. In a face-to-face setting the merchant can inspect the card to ensure that it is valid and can verify that the cardholder is an authorized user on the account. None of these actions can be performed when the payment is submitted online or accepted by phone. As we moved in adopting EMV Technology, majority of fraud is going to migrate away from counterfeit and stolen cards towards the card-not-present transaction as happened in other countries.
A combination of best practices and fraud prevention tools can provide card-not-present merchants with strong fraud prevention capabilities.
Steps to avoid fraud and protect your business for a card-not-present transaction:
- Email Verification: Send a message to the email address provided by the customer requesting that the customer verify the email address is correct, you can ensure that the email is associated with the other information provided.
- Maintain PCI compliance:All merchants accepting card payments are now required to be compliant with the requirements of the PCI DSS (Payment Card Industry Data Standard) which sets the rules for data security management, policies, procedures, network architecture, software design and other protective measures.
- Security Code Verification. Requesting the three digit security code on the back of a credit card. Visa (CVV2), MasterCard (CVC 2) and Discover (CID) cards, and the 4-digit numbers located on the front of American Express (CID) cards. Card Security Codes help verify that the customer is in a physical possession of a valid card during a card-not-present transaction.
- Use an Address Verification Service (AVS): Enables you to compare the billing address provided by your customer with the billing address on the card issuer’s file before processing a transaction. AVS is good protection against card information obtained through means like phishing and malware because fraudster might not know the billing address.
- Use 3D Secure Service: MasterCard and Verified by Visa enable cardholders to authenticate themselves to their card issuers through the use of personal passwords they create when they register their cards with the programs. The liability of any fraudulent charges through the 3D service is picked up by the issuer, not the merchant.
- Verify the phone number and transaction information.Prior to shipping your products, call the phone number provided by the customer and verify the transaction information. Criminals may be unable to verify such information, because in their haste to max out the credit line before the fraud is discovered, they often order at random and do not keep records.
Posted in Best Practices for Merchants, e-commerce & m-commerce, Mail Order Telephone Order, Payment Card Industry PCI Security, Travel Agency Agents Tagged with: American Express, card-not-present, card-security, cardholder, cnp, credit card, Discover, EMV, MasterCard, merchant, Payment Card Industry, payments, PCI, visa
All merchants that accepts, transmit or stores cardholder data are required to be PCI (Payment Card Industry) Compliant. Most believe that because they do not charge the credit cards themselves, they are exempt. Why all agencies are required to be complaint even when they don’t charge credit cards themselves, and some steps to ensure your agency is PCI compliant.
What is PCI compliance?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements designed to ensure that all companies that process, store or transmit credit card information maintain a secure environment. PCI applies to all organizations or merchants, regardless of size or number of transactions, that accepts, transmits or stores any cardholder data. Travel agents accepting, storing and transmitting credit card information to suppliers, are required to be compliant too. Suppliers reinforce this through their travel agent guidelines/contracts. Travel Agency must adhere to the applicable credit card company’s procedures for credit card transactions.
Consequences of Not Being PCI Compliant
If an agency is not PCI compliant, the agency can lose the ability to process credit card payments with that supplier. Not being able to pay with client credit cards can be a serious roadblock for agencies, and an inconvenience for clients.
If you have a merchant account and are found to be out of compliance, you can be fined.
How to be PCI Compliant
Don’t store the CCV security code from the client’s credit card. The client does not have the authority to grant you permission to store their CCV code. The credit card company explicitly forbid storage of the CCV code.
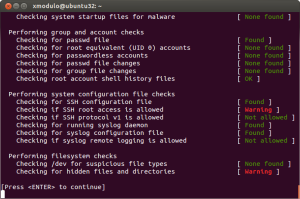
Make sure you securely store any client information, including their credit card number and expiration date. If you use a CRM, ensure that you have a strong password. If your CRM database is stored on your computer hard drive, encrypt it (there is a great encryption software that is free of charge). If you have an IT resource, talk to them about installing a firewall on your network, installing anti-virus and anti-malware protection, and any other steps that you can take to secure your client data even further.
If you keep paper copies of client information, keep it in a locked filing cabinet or desk drawer. When you no longer need their credit card information, cross shred it.
Home based businesses are arguably the most vulnerable simply because they are usually not well protected, according to the PCI Compliance Guide. Having strong passwords, encryption, a firewall, anti-virus and anti-malware protection are all inexpensive steps that you can take to protect your business and your clients’ sensitive data.
If you receive a courtesy call reminding you about PCI Compliance, don’t ignore it.
Posted in Best Practices for Merchants, Credit card Processing, Credit Card Security, Payment Card Industry PCI Security Tagged with: cardholder, cardholder data, cards, CCV, CCV code, credit, credit card company, credit card number, credit card payments, credit card transactions, credit cards, crm, CRM database, data, database, encryption software, merchant account, Merchant's, network, Payment Card Industry, PCI, security code, transactions, travel agents
October 8th, 2014 by Elma Jane
When the PCI Security Standards Council (PCI SSC) launched PCI DSS v3.0 in January 2014, businesses were given one year to implement the updated global standard. Now that the deadline is fast approaching, interest is picking up in what v3.0 entails. On Jan. 1, 2015, version 3.0 of the Payment Card Industry (PCI) Data Security Standard (DSS) will reach year one of its three-year lifecycle.
Trustwave, a global data security firm, is on the frontlines of helping secure the networks of merchants and other businesses on the electronic payments value chain against data breaches. As an approved scanning vendor, Trustwave is used by businesses to achieve and validate PCI DSS compliance.
PCI DSS v3.0 is business as usual for the most part, except for a few changes from v2.0 that considers impactful for large swaths of merchants. The top three changes involve e-commerce businesses that redirect consumers to third-party payment providers. The expansion of penetration testing requirements and the data security responsibilities of third-party service providers.
Penetration testing
Penetration testing is the way in which merchants can assess the security of their networks by pretending to be hackers and probing networks for weaknesses. V3.0 of the PCI DSS mandates that merchants follow a formal methodology in conducting penetration tests, and that the methodology goes well beyond what merchants can accomplish using off-the-shelf penetration testing software solutions.
Merchants that are self assessing and using such software are going to be surprised by the rigorous new methodology they are now expected to follow.
Additionally, penetration testing requirements in v3.0 raises the compliance bar for small merchants who self assess. Those merchants could lower the scope of their compliance responsibilities by segmenting their networks, which essentially walls off data-sensitive areas of networks from the larger network. In this way merchants could reduce their compliance burdens and not have to undergo penetration testing.
Not so in v3.0. If you do something to try to reduce the scope of the PCI DSS to your systems, you now need to perform a penetration test to prove that those boundaries are in fact rigid.
Redirecting merchants
The new redirect mandate as affecting some, but not all, e-commerce merchants that redirect customers, typically when they are ready to pay for online purchases to a third party to collect payment details. If you are a customer and you are going to a website and you add something to your shopping cart, when it comes time to enter in your credit card, this redirect says I’m going to send you off to this third party.
The redirect can come in several forms. It can be a direct link from the e-commerce merchant’s website to another website, such as in a PayPal Inc. scenario, or it can be done more silently.
An example of the silent method is the use of an iframe, HTML code used to display one website within another website. Real Estate on the merchant’s website is used by the third-party in such a way that consumers don’t even know that the payment details they input are being collected and processed, not by the e-commerce site, but by the third party.
Another redirect strategy is accomplished via pop-up windows for the collection of payments in such environments as online or mobile games. In-game pop-up windows are typically used to get gamers to pay a little money to purchase an enhancement to their gaming avatars or advance to the next level of game activity.
For merchants that employ these types of redirect strategies, PCI DSS v3.0 makes compliance much more complicated. In v2.0, such merchants that opted to take Self Assessment Questionnaires (SAQs), in lieu of undergoing on-site data security assessments, had to fill out the shortest of the eight SAQs. But in v3.0, such redirect merchants have to take the second longest SAQ, which entails over 100 security controls.
The PCI SSC made this change because of the steady uptick in the number and severity of e-commerce breaches, with hackers zeroing in on exploiting weaknesses in redirect strategies to steal cardholder data. Also, redirecting merchants may be putting themselves into greater data breach jeopardy when they believe that third-party payment providers on the receiving end of redirects are reducing merchants’ compliance responsibilities, when that may not, in fact, be the case.
Service providers
Service provider is any entity that stores, processes or transmits payment card data. Examples include gateways, web hosting companies, back-up facilities and call centers. The update to the standard directs service providers to clearly articulate in writing which PCI requirements they are addressing and what areas of the PCI DSS is the responsibility of merchants.
A web hosting company may tell a merchant that the hosting company is PCI compliant. The merchant thought, they have nothing left to do. The reality is there is still always something a merchant needs to do, they just didn’t always recognize what that was.
In v3.0, service providers, specifically value-added resellers (VARs), also need to assign unique passwords, as well as employ two-factor authentication, to each of their merchants in order to remotely access the networks of those merchants. VARs often employ weak passwords or use one password to access multiple networks, which makes it easier for fraudsters to breach multiple systems.
The PCI SSC is trying to at least make it more difficult for the bad guys to break into one site and then move to the hub, so to speak, and then go to all the other different spokes with the same attack.
Overall, v3.0 is more granular by more accurately matching appropriate security controls to specific types of merchants, even though the approach may add complexity to merchants’ compliance obligations. On the whole a lot of these changes are very positive.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security Tagged with: (PCI SSC), call centers, cardholder data, consumers, credit-card, customers, data breaches, data security assessments, Data Security Standard, e-commerce breaches, e-commerce businesses, e-commerce merchant's website, electronic payments, global data security, global standard, Merchant's, merchant’s website, mobile, networks, payment, payment card data, Payment Card Industry, payment providers, PCI Security Standards Council, PCI-DSS, Penetration testing, Service providers, shopping cart, software solutions, web hosting, website
September 24th, 2014 by Elma Jane
The CVV Number (Card Verification Value) on your credit card or debit card is a 3 digit number on VISA, MasterCard and Discover branded credit and debit cards. On your American Express branded credit or debit card it is a 4 digit numeric code.
The codes have different names:
American Express – CID or unique card code.
Debit Card – CSC or card security code.
Discover – card identification number (CID)
Master Card – card validation code (CVC2)
Visa – card verification value (CVV2)
CVV numbers are NOT your card’s secret PIN (Personal Identification Number).
You should never enter your PIN number when asked to provide your CVV. (PIN numbers allow you to use your credit or debit card at an ATM or when making an in-person purchase with your debit card or a cash advance with any credit card.)
Types of security codes:
CVC1 or CVV1, is encoded on track-2 of the magnetic stripe of the card and used for card present transactions. The purpose of the code is to verify that a payment card is actually in the hand of the merchant. This code is automatically retrieved when the magnetic stripe of a card is swiped on a point-of-sale (card present) device and is verified by the issuer. A limitation is that if the entire card has been duplicated and the magnetic stripe copied, then the code is still valid.
The most cited, is CVV2 or CVC2. This code is often sought by merchants for card not present transactions occurring by mail or fax or over the telephone or Internet. In some countries in Western Europe, card issuers require a merchant to obtain the code when the cardholder is not present in person.
Contactless card and chip cards may supply their own codes generated electronically, such as iCVV or Dynamic CVV.
Code Location:
The card security code is typically the last three or four digits printed, not embossed like the card number, on the signature strip on the back of the card. On American Express cards, the card security code is the four digits printed (not embossed) on the front towards the right. The card security code is not encoded on the magnetic stripe but is printed flat.
American Express cards have a four-digit code printed on the front side of the card above the number.
MasterCard, Visa, Diners Club, Discover, and JCB credit and debit cards have a three-digit card security code. The code is the final group of numbers printed on the back signature panel of the card.
New North American MasterCard and Visa cards feature the code in a separate panel to the right of the signature strip. This has been done to prevent overwriting of the numbers by signing the card.
Benefits when it comes to security:
As a security measure, merchants who require the CVV2 for card not present payment card transactions are required by the card issuer not to store the CVV2 once the individual transaction is authorized and completed. This way, if a database of transactions is compromised, the CVV2 is not included, and the stolen card numbers are less useful. Virtual Terminals and payment gateways do not store the CVV2 code, therefore employees and customer service representatives with access to these web-based payment interfaces who otherwise have access to complete card numbers, expiration dates, and other information still lack the CVV2 code.
The Payment Card Industry Data Security Standard (PCI DSS) also prohibits the storage of CSC (and other sensitive authorization data) post transaction authorization. This applies globally to anyone who stores, processes or transmits card holder data. Since the CSC is not contained on the magnetic stripe of the card, it is not typically included in the transaction when the card is used face to face at a merchant. However, some merchants in North America require the code. For American Express cards, this has been an invariable practice (for card not present transactions) in European Union (EU) states like Ireland and the United Kingdom since the start of 2005. This provides a level of protection to the bank/cardholder, in that a fraudulent merchant or employee cannot simply capture the magnetic stripe details of a card and use them later for card not present purchases over the phone, mail order or Internet. To do this, a merchant or its employee would also have to note the CVV2 visually and record it, which is more likely to arouse the cardholder’s suspicion.
Supplying the CSC code in a transaction is intended to verify that the customer has the card in their possession. Knowledge of the code proves that the customer has seen the card, or has seen a record made by somebody who saw the card.
Posted in Best Practices for Merchants, EMV EuroPay MasterCard Visa, Point of Sale, Visa MasterCard American Express Tagged with: (Card Verification Value), (CVC2), American Express, atm, authorization data, bank/cardholder, card holder data, card identification number, card issuers, Card Not Present transactions, card number, card numbers, card security code, card validation code, card-not-present, card-present transactions, cardholder, cards, cash advance, chip cards, CID, code, Contactless card, credit, credit-card, CSC, customer, customer service, CVC1, CVV Number, CVV1, CVV2, Data Security Standard, debit, debit card, debit cards, device, Diners Club, Discover, fax, gateways, iCVV or Dynamic CVV, individual transaction, internet, issuer, JCB credit, magnetic stripe, mail, MasterCard, merchant, payment card, Payment Card Industry, payment card transactions, payment gateways, PCI-DSS, Personal Identification Number, PIN, point of sale, post transaction authorization, security codes, telephone, terminals, unique card code, virtual terminals, visa, web-based payment
September 10th, 2014 by Elma Jane
If your businesses considering an iPad point-of-sale (POS) system, you may be up for a challenge. Not only can the plethora of providers be overwhelming, but you must also remember that not all iPad POS systems are created equal. iPad POS systems do more than process payments and complete transactions. They also offer advanced capabilities that streamline operations. For instance, they can eliminate manual data entry by integrating accounting software, customer databases and inventory counts in real time, as each transaction occurs. With these systems, you get 24/7 access to sales data without having to be in the store. The challenge, however, is knowing which provider and set of features offer the best iPad POS solution for your business. iPad POS systems vary in functionality far more than the traditional POS solutions and are often targeted at specific verticals rather than the entire market. For that reason, it’s especially important to compare features between systems to ultimately select the right system for your business.
To help you choose a provider, here are things to look for in an iPad POS system.
Backend capabilities
One of the biggest benefits of an iPad POS system is that it offers advanced features that can streamline your entire operations. These include backend processes, such as inventory tracking, data analysis and reporting, and social media integration. As a small business, two of the most important time saving and productivity-boosting features to look for are customer relationship management (CRM) capabilities and connectivity to other sales channels. You’ll want an iPad POS that has robust CRM and a customizable customer loyalty program. It should tell you which products are most and least frequently purchased by specific customers at various store locations. It should also be able to identify the frequent VIP shoppers from the less frequent ones at any one of your store locations, creating the ultimate customer loyalty program for the small business owner. If you own an online store or use a mobile app to sell your products and services, your iPad POS software should also be able to integrate those online platforms with in-store sales. Not only will this provide an automated, centralized sales database, but it can also help increase total sales. You should be able to sell effortlessly through online, mobile and in-store channels. Why should your customers be limited to the people who walk by your store? Your iPad POS should be able to help you sell your products through more channels, online and on mobile. E-commerce and mobile commerce (mCommerce) aren’t just for big box retailers.
Cloud-based
The functions of an iPad POS solution don’t necessarily have to stop in-store. If you want to have anytime, anywhere access to your POS system, you can use one of the many providers with advanced features that give business owners visibility over their stores, its records and backend processes using the cloud. The best tablet-based POS systems operate on a cloud and allow you to operate it from any location you want. An iPad POS provider, with a cloud-based iPad POS system, businesses can keep tabs on stores in real time using any device, as well as automatically back up data. This gives business owners access to the system on their desktops, tablets or smartphones, even when not inside their stores. Using a cloud-based system also protects all the data that’s stored in your point of sale so you don’t have to worry about losing your data or, even worse, getting it stolen. Because the cloud plays such a significant role, businesses should also look into the kind of cloud service an iPad POS provider uses. In other words, is the system a cloud solution capable of expanding, or is it an app on the iPad that is not dependent on the Internet? Who is the cloud vendor? Is it a premium vendor? The type of cloud a provider uses can give you an idea about its reliability and the functions the provider will offer.
Downtime and technical support
As a small business, you need an iPad POS provider that has your back when something goes wrong. There are two types of customer support to look for: Downtime support and technical support.
iPad POS systems are often cheaper and simpler than traditional systems, but that doesn’t mean you can ignore the product support needs. The POS is a key element of your business and any downtime will likely result in significant revenue loss. You could, for instance, experience costly downtime when you lose Internet connectivity. iPad POS systems primarily rely on the Web to perform their core functions, but this doesn’t mean that when the Internet goes down, your business has to go down, too. Many providers offer offline support to keep your business going, such as Always on Mode. The Always on Mode setting enables your business to continue running even in the event of an Internet outage. Otherwise, your business will lose money during a loss of connectivity. Downtime can also happen due to technical problems within the hardware or software. Most iPad POS providers boast of providing excellent tech support, but you never really know what type of customer service you’ll actually receive until a problem occurs.
Test the friendliness of customer service reps by calling or emailing the provider with questions and concerns before signing any contracts. This way, you can see how helpful their responses are before you purchase their solution. Your POS is the most important device in your store. It’s essentially the gateway to all your transactions, customer data and inventory. If anything happens to it, you’ll need to be comfortable knowing that someone is there to answer your questions and guide you through everything.
Grows with your business
All growing businesses need tech solutions that can grow right along with them. Not all iPad POS systems are scalable, so look for a provider that makes it easy to add on more terminals and employees as your business expands. Pay attention to how the software handles growth in sales and in personnel. As a business grows, so does it sales volume and the required software capabilities. Some iPad POS solutions are designed for very small businesses, offering very limited features and transactions. If you have plans for growth, look for a provider that can handle the changes in transactions your business will be going through. Find out about features and customization. Does the system do what you want it to do? Can it handle large volume? How much volume? What modules can you add, and how do you interface to third parties? You should also consider the impacts of physical expansion and adding on new equipment and employees. If there are plans in the future for you to open another store location, you’ll need to make sure that your point of sale has the capabilities of actually handling another store location without adding more work for you. If you plan on hiring more employees for your store, you’ll also want to know that the solution you choose can easily be learned, so onboarding new staff won’t take up too much of your time.
Security
POS cyber attacks have risen dramatically over the past couple of years, making it more critical than ever to protect your business. Otherwise, it’s not just your business information at risk, but also your reputation and entire operations. iPad POS system security is a bit tricky, however. Unlike credit card swipers and mobile credit card readers that have long-established security standards namely, Payment Card Industry (PCI) compliance — the criteria for the iPad hardware itself as a POS terminal aren’t quite so clear-cut. Since iPads cannot be certified as PCI compliant, merchants must utilize a point-to-point encryption system that leaves the iPad out of scope. This means treating the iPad as its own system, which includes making sure it doesn’t save credit-card information or sensitive data on the iPad itself. To stay protected, look for PCI-certified, encrypted card swipers.
Posted in Best Practices for Merchants, Mobile Point of Sale, Point of Sale Tagged with: (POS) systems, accounting, app, business, card, cloud-based, credit, credit card readers, credit-card, crm, customer, customer relationship management, customer support, data, data analysis, database, desktops, e-commerce, inventory, iPad Point-Of-Sale, loyalty program, mcommerce, mobile, mobile app, mobile commerce, online, online platforms, Payment Card Industry, payments, PCI, platforms, POS, POS solution, products, sales, Security, security standards, services, Smartphones, social media, software, tablets, terminal, transactions, web
August 27th, 2014 by Elma Jane
Backoff malware that has attacked point of sale systems at hundreds of businesses may accelerate adoption of EMV chip and PIN cards and two-factor authentication as merchants look for ways to soften the next attack. Chip and PIN are a big thing, because it greatly diminishes the value of the information that can be trapped by this malware, said Trustwave, a security company that estimates about 600 businesses have been victims of the new malware. The malware uses infected websites to infiltrate the computing devices that host point of sale systems or are used to make payments, such as PCs, tablets and smartphones. Merchants can install software that monitors their payments systems for intrusions, but the thing is you can’t just have anti-virus programs and think you are safe. Credit card data is particularly vulnerable because the malware can steal data directly from the magnetic stripe or keystrokes used to make card payments.
The point of sale system is low-hanging fruit because a lot of businesses don’t own their own POS system. They rent them, or a small business may hire a third party to implement their own point of sale system. The Payment Card Industry Security Standards Council issued new guidance this month to address security for outsourced digital payments. EMV-chip cards, which are designed to deter counterfeiting, would gut the value of any stolen data. With this magnetic stripe data, the crooks can clone the card and sell it on the black market. With chip and PIN, the data changes for each transaction, so each transaction is unique. Even if the malware grabs the data, there not a lot the crooks can do with it. The EMV transition in the U.S. has recently accelerated, driven in part by recent highprofile data breaches. Even with that momentum, the U.S. may still take longer than the card networks’ October 2015 deadline to fully shift to chip-card acceptance.
EMV does not by itself mitigate the threat of breaches. Two-factor authentication, or the use of a second channel or computing device to authorize a transaction, will likely share in the boost in investment stemming from data security concerns. The continued compromise of point of sale merchants through a variety of vectors, including malware such as Backoff, will motivate the implementation among merchants of stronger authentication to prevent unauthorized access to card data.
Backoff has garnered a lot of attention, including a warning from the U.S. government, but it’s not the only malware targeting payment card data. It is not the types of threats which are new, but rather the frequency with which they are occurring which has put merchants on their heels. There is also an acute need to educate small merchants on both the threats and respective mitigation techniques.. The heightened alert over data vulnerability should boost the card networks’ plans to replace account numbers with substitute tokens to protect digital payments. Tokens would not necessarily stop crooks from infiltrating point of sale systems, but like EMV technology, they would limit the value of the stolen data. There are two sides to the equation, the issuers and the merchants. To the extent we see both sides adopt tokenization, you will see fewer breaches and they will be less severe because the crooks will be getting a token instead of card data.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security, Point of Sale Tagged with: access, account, account numbers, anti-virus programs, authentication, Backoff, card, card networks, chip, credit, Credit card data, credit-card, data, data breaches, devices, digital payments, EMV, magnetic stripe, Malware, Merchant's, Payment Card Industry, payments, PCs, PIN, PIN cards, point of sale, POS, POS system, programs, Security, security standards, Smartphones, software, system, tablets, tokenization, tokens, transaction, Trustwave, websites
August 11th, 2014 by Elma Jane
Tokenization technology has been available to keep payment card and personal data safer for several years, but it’s never had the attention it’s getting now in the wake of high-profile breaches. Still, merchants especially smaller ones haven’t necessarily caught on to the hacking threat or how tools such as tokenization limit exposure. That gap in understanding places ISOs and agents in an important place in the security mix, it’s their job to get the word out to merchants about the need for tokenization. That can begin with explaining what it is.
The biggest challenge that ISOs will see and are seeing, is this lack of awareness of these threats that are impacting that business sector. Data breaches are happening at small businesses, and even if merchants get past the point of accepting that they are at risk, they have no clue what to do next. Tokenization converts payment card account numbers into unique identification symbols for storage or for transactions through payment mechanisms such as mobile wallets. It’s complex and not enough ISOs understand it, even though it represents a potential revenue-producer and the industry as a whole is confused over tokenization standards and how to deploy and govern them.
ISOs presenting tokenization to merchants should echo what security experts and the Payment Card Industry Security Council often say about the technology. It’s a needed layer of security to complement EMV cards. EMV takes care of the card-present counterfeit fraud problem, while tokenization deters hackers from pilfering data from a payment network database. The Target data breach during the 2013 holiday shopping season haunts the payments industry. If Target’s card data had been tokenized, it would have been worthless to the criminals who stole it. It wouldn’t have stopped malware access to the database, but it would been as though criminals breaking into a bank vault found, instead of piles of cash, poker chips that only an authorized user could cash at a specific bank.
A database full of tokens has no value to criminals on the black market, which reduces risk for merchants. Unfortunately, the small merchants have not accepted the idea or the reality and fact, that there is malware attacking their point of sale and they are being exposed. That’s why ISOs should determine the level of need for tokenization in their markets. It is always the responsibility of those who are interacting with the merchant to have the knowledge for the market segment they are in. If you are selling to dry cleaners, you probably don’t need to know much about tokenization, but if you are selling to recurring billing or e-commerce merchants, you probably need a lot more knowledge about it.
Tokenization is critical for some applications in payments. Any sort of recurring billing that stores card information should be leveraging some form of tokenization. Whether the revenue stream comes directly from tokenization services or it is bundled into the overall payment acceptance product is not the most important factor. The point is that it’s an important value to the merchant to be able to tokenize the card number in recurring billing, but ISOs sell tokenization products against a confusing backdrop of standards developed for different forms of tokenization. EMVCo, which the card brands own, establishes guidelines for EMV chip-based smart card use. It’s working on standards for “payment” tokenization with the Clearing House, which establishes payment systems for financial institutions. Both entities were working on separate standards until The Clearing House joined EMVCo’s tokenization working group to determine similarities and determine whether one standard could cover the needs of banks and merchants.
Posted in Best Practices for Merchants Tagged with: account numbers, bank, billing, card, card brands, card number, card present, Clearing House, data, data breaches, database, e-commerce, EMV, emvco, fraud, ISOs, Malware, Merchant's, mobile wallets, network, payment, Payment Card Industry, Security, smart card, target, tokenization, transactions