August 7th, 2014 by Elma Jane
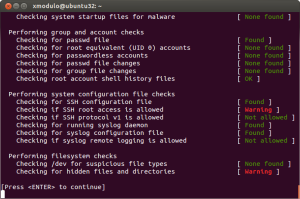
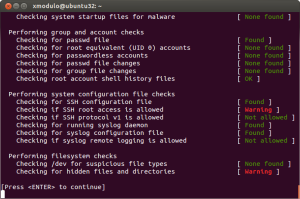
Recent high-profile cyberattacks at retail giants like Target and Neiman Marcus have highlighted the importance of protecting your business against point-of-sale (POS) security breaches. Often, the smallest merchants are the most vulnerable to these types of cyberthreats. The latest of these POS attacks is known as Backoff, a malware with such brute force that the U.S. Department of Homeland Security (DHS) has gotten involved. The DHS recently released a 10-page advisory that warns retailers about the dangers of Backoff and tells them how they can protect their systems. Backoff and its variants are virtually undetectable low to zero percent by most antivirus software, thus making it more critical for retailers to make sure their networks and POS systems are secure.
How Backoff works
Backoff infiltrates merchant computer systems by exploiting remote desktop applications, such as Microsoft’s Remote Desktop, Apple Remote Desktop, Chrome Remote Desktop, Splashtop 2 and LogMeIn, among others. Attackers then use these vulnerabilities to gain administrator and privileged access to retailer networks. Using these compromised accounts, attackers are able to launch and execute the Backoff malware on POS systems. The malware then makes its way into computer and network systems, gathers information and then sends the stolen data to cybercriminals. The advisory warns that Backoff has four capabilities that enable it to steal consumer credit card information and other sensitive data: scraping POS and computer memory, logging keystrokes, Command & Control (C2) communication, and injecting the malware into explorer.exe. Although Backoff is a newly detected malware, forensic investigations show that Backoff and its variants have already struck retailers three times since 2013, the advisory revealed. Its known variants include goo, MAY, net and LAST.
Prevent a Backoff attack
To mitigate and prevent Backoff malware attacks, the DHS’ recommendations include the following:
Configure network security. Reevaluate IP restrictions and allowances, isolate payment networks from other networks, use data leakage and compromised account detection tools, and review unauthorized traffic rules.
Control remote desktop access. Limit the number of users and administrative privileges, require complex passwords and two-factor authentication, and automatically lock out users after inactivity and failed login attempts.
Implement an incident response system. Use a Security Information and Event Management (SIEM) system to aggregate and analyze events and have an established incident response team. All logged events should also be stored in a secure, dedicated server that cannot be accessed or altered by unauthorized users.
Manage cash register and POS security. Use hardware-based point-to-point encryption, use only compliant applications and systems, stay up-to-date with the latest security patches, log all events and require two-factor authentication.
Posted in Point of Sale Tagged with: (POS) systems, antivirus software, Apple Remote Desktop, Backoff, cash register, Chrome Remote Desktop, credit-card, cyber attacks, cybercriminals, data, data leakage, Department of Homeland Security, desktop applications, DHS, goo, LAST, LogMeIn, Malware, MAY, Merchant's, Microsoft's, Neiman Marcus, net, network security, network systems, networks, payment networks, point of sale, point-to-point encryption, POS, remote, retailer networks, retailers, security breaches, Splashtop 2, target
May 6th, 2014 by Elma Jane
Which fee structure works best remains unclear despite the recent high-profile data security breaches that are emphasizing the need for security measures. Acquirers charge fees – or not – based on what’s best for their business model and their security objectives
Some charge merchants that comply, others charge merchants that fail to comply and a few charge both. Some Independent Sales Organizations (ISOs) don’t charge merchants a fee for helping them comply with the Payment Card Industry data security standards (PCIS DSS).
If there is any trend, it’s that more banks are finding that some sort of funding is necessary to run a program that gets any results. That funding covers costs for security assessments and compliance assistance as well as internal resources for acquirers. When it comes to covering those costs and creating incentives for compliance, no one fee structure is ideal.
Non-compliance fees encourage merchants to comply so they can save money, but the fees may not accomplish that. Unless you charge exorbitantly, it’s not going to have the effect you want it to have, and by the time you charge that much, the merchant’s just going to move to a different ISO.
ISOs charging non-compliance fees often claim the fee revenue goes into an account designated for use in case of a breach. Non-compliance fees can also reward acquirers for doing nothing to increase compliance. You get this situation where a bank has a revenue stream. Their objective is not to increase the revenue stream but to increase compliance, when they increase compliance, the revenue stream goes down.
It is recommended to some acquirers that they consider charging merchants fees for doing things like storing card data, which could be checked with a scanning tool. Merchants that do store data or fail to run the scan would be charged a fee. That is something that could really decrease risk, because if you’re not storing card data, even if you are breached, there’s nothing to get.
Simplifying the compliance verification process, by making assessment questionnaires available on its merchant portal and by teaching merchants about PCI, will minimize the potential impact of fraud by increasing compliance, which saves the company money in the long run versus a more laissez-faire approach of fees without education and compliance tools.
It’s more important to educate the merchant, it’s the spirit and intent of PCI-DSS supported by the card associations. Visa and MasterCard support it because of the severe impact of a breach or other data compromise, not as a revenue source.
ISOs and other players in the payments chain that do not work to help merchants comply are also putting themselves at risk. Breached merchants may be unable to pay fines that come with a data compromise, potentially leaving ISOs responsible for paying them. Merchants that go out of business because of a data breach also stop providing the ISO with revenue.
Plus, when merchants ask why they’re being charged a non-compliance fee, point them to the questionnaire and explain that they’ll stop being charged as soon as they demonstrate they comply with PCI.
Posted in Best Practices for Merchants, Credit Card Security, Merchant Account Services News Articles, Payment Card Industry PCI Security Tagged with: card associations, card data, compliance, compliance fee, data, data security standards, ISOs, MasterCard, Merchant's, Payment Card Industry, portal, security breaches, visa